Tech terminologies are words or a set of words that are used in technical fields. One of the fields where technological terminologies are used widely is IT. These terms can be any word that has a specialized meaning. For newcomers in any field, it is beneficial to know the terminologies as they aid in communication among colleagues and professionals. This blog will discuss many of the terminologies used in IT sectors for newcomers helping them to fit in the environment.
1- Algorithm
A collection of instructions or rules provided to accomplish a particular task or address a category of problems or computations. The main purpose that an algorithm serves is data processing and performing calculations. Due to recent advancements in AI, the utilization of algorithms has witnessed a notable increase.
2- Software
Software is a general term for different kinds of programs that tell the computer to perform specified tasks. A software can be a system software or an application software. Each software consists of user manuals for users on the functioning of the software.
3- Hardware
Computer hardware consists of the actual components of a computer. The components of the computer i.e. casing, central processing unit, random access memory, monitor, mouse, keyboard, hard drive, and motherboard. These components store and execute the set of instructions that a software constitutes.
4- Programming Language
A formal system used to instruct computers, such as Python, Java, or C++. Each programming language consists of syntaxes and semantics and each language has its properties and functioning.
5- Code
Code is simply words or phrases written in a programming language that a computer can execute. In communication and information processing, a code is a set of rules converting information into a different form, often abbreviated, or encrypted, for transmission through a channel or storage in a medium.
6- Database
A database is a collection of organized information or a type of data repository that works with a database management system. This software interacts with end users, applications, and the database to capture and propose information. The purpose of a database is also to secure information and retrieve it again.
7- Cloud Computing
Cloud computing refers to the immediate accessibility of computer system resources. It aids in accessing data storage and computational capacity without direct user intervention. Extensive cloud networks frequently distribute functions across various locations with each serving as a data centre.
8- Cybersecurity
Computer security, also known as cybersecurity, involves the safety of computing systems and networks against malicious attacks or unauthorized access. These malicious attacks could lead to the disclosure of unauthorized information, theft, or damage to hardware, software, or data. Additionally, it aims to avoid any interference or misdirection of the services offered by these systems.
9 – Encryption
Encryption is the procedure of transforming information and converting the plaintext into an alternative form termed ciphertext. Only authorized parties can decipher ciphertext back into plaintext while ensuring access to the original information.
10 – API
An application programming interface (API) serves as a mechanism for two or more computer programs or components to communicate effectively. It provides a service to other software components functioning as a software interface.
11- HTML
Hypertext Markup Language (HTML) serves the purpose of the conventional markup language for creating and designing web pages. As a markup language, it documents things intended to be presented in a web browser. It sets out the content and structure of web content and is frequently complemented by technologies like Cascading Style Sheets and scripting languages such as JavaScript.
As a markup language, it’s used to write things meant to be shown on a web browser.
12- URL
A Uniform Resource Locator (URL) is like a web link and shows where something is on the internet and how to get it. The most used terminologies used by people are URL and web address interchangeably.
13- Cache
Cache is a storage space in either hardware or software that keeps information, helping to quickly provide data when it’s requested again, making things faster. The data in a cache could be from a previous calculation or a copy of information saved in another place. In general, we can say that temporary storage helps to retrieve data quickly, reducing the need to access the source cache.
14- Artificial intelligence
Artificial intelligence is the enchanting realm where machines and software collect a form of intellect, distinct from the intelligence found in humans. Artificial Intelligence unfolds as an art exploring the intricacies of intelligent machines.
15- Machine Learning
Machine learning, which is a field of study in computer science and artificial intelligence, concentrates on developing and studying statistical algorithms. These algorithms learn from data and, akin to humans, refine their accuracy over time. This enables them to perform tasks without explicit instructions.
16- Deep Learning
Deep learning is a segment of machine learning and artificial intelligence that utilizes artificial neural networks with multiple layers for representation learning. It replicates the human brain’s ability to process data and enables systems to autonomously learn, identify patterns, and perform intricate tasks with increased accuracy and as a result, reduce the need for human intervention. This approach makes deep learning a powerful method inspired by human cognitive processes.
17- Metadata
Metadata is information about other data, not the content of the data itself, such as the text of a message or the image. It serves as a structured reference, aiding in the sorting and identification of attributes associated with the described information. This provides details about a resource, offering context about the source, type, owner, and relationships.
18- Blockchain
Blockchain is an advanced database mechanism in a business network, providing a collective and unchangeable ledger for documenting transactions and monitoring assets. It enables transparent information sharing, with data stored in interconnected blocks forming a chain. Whether tangible or intangible assets, almost anything of worth can be monitored and exchanged on a blockchain network, reducing risks and costs. The chronological consistency of the blockchain database ensures an unalterable ledger for tracking various transactions, offering security and decentralization beyond its role in cryptocurrency systems.
19- IoT
The Internet of Things (IoT) deals with devices that have processing abilities, sensors, software, and other technologies. These devices connect and exchange data with other devices and systems using the Internet or other communication networks. IoT comprises a combination of electronics and networking engineering
20- Operating System (OS)
An operating system is software that manages computer hardware and provides services for computer programs. It acts as an intermediary between users and the computer hardware, facilitating communication and execution of tasks.

21- Firewall
A firewall is a security system that monitors and controls incoming and outgoing network traffic based on predetermined security rules. It acts as a barrier to prevent unauthorized access and protect against potential cyber threats.
22- VPN (Virtual Private Network)
A VPN is a technology that creates a secure, encrypted connection over a less secure network, such as the Internet. It allows users to access private networks and share data remotely while maintaining confidentiality and security.
23- Server
A server is a computer or system that provides services, resources, or data to other computers, known as clients, over a network. Servers can handle various tasks such as hosting websites, managing emails, or storing files.
24- Bug
A bug is a programming error or flaw that causes a software program to behave unexpectedly or produce incorrect results. Debugging is the process of identifying and fixing bugs in a program.
25- Interface
An interface is a point of interaction between different software components or between a user and a computer system. It defines how users or programs can interact with and utilize the features of a software application
Don't know where to start your tech career?
We are here for you! Schedule a free call with our consultant for personalized advice on achieving your learning goals
26- LAN (Local Area Network)
A LAN is a network of interconnected computers and devices within a limited geographic area, such as an office or a home. It enables the sharing of resources and information among connected devices.
27- WAN (Wide Area Network)
A WAN is a network that spans a larger geographic area, connecting multiple LANs. It allows communication between devices over longer distances, often using external communication lines.
28- Backup
Backup refers to the process of creating copies of important data to prevent loss in case of hardware failure, accidental deletion, or other unforeseen events. Regular backups are crucial for data recovery and system reliability.
29- GUI (Graphical User Interface)
GUI is a visual interface that allows users to interact with electronic devices or software through graphical elements such as icons, buttons, and menus. It simplifies user interaction and enhances user experience.
30- Serverless Computing
Serverless computing is a cloud computing model where cloud providers automatically manage infrastructure, allowing developers to focus solely on writing code without the need to manage servers. It is cost-effective and scalable.
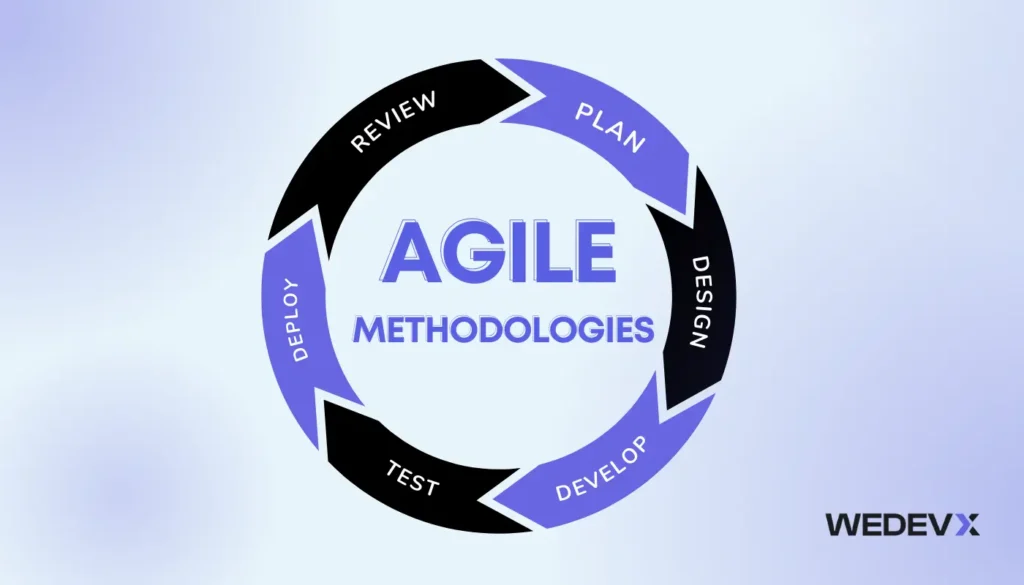
31- Scrum
Scrum is an agile project management framework used in software development. It emphasizes collaboration, flexibility, and iterative progress in project development, promoting adaptability to changing requirements.
32- API Gateway
An API Gateway is a server that acts as an API front-end, receiving API requests, enforcing throttling, and routing them to the appropriate microservices. It plays a crucial role in managing and securing API communication.
33- Open Source
Open source refers to software whose source code is freely available to the public. Users can view, modify, and distribute the code, fostering collaboration and community-driven development.
34- Agile Development
Agile development is a methodology that promotes iterative development, collaboration, and adaptability to changing requirements. It emphasizes delivering functional software in short, incremental cycles.
35- DevOps
DevOps is a set of practices that combines software development (Dev) and IT operations (Ops) to enhance collaboration and productivity. It aims to automate and streamline the software development lifecycle.
36- Containerization
Containerization involves encapsulating an application and its dependencies into a lightweight container. Containers provide consistency across different development, testing, and deployment environments.
37- Microservices
Microservices is an architectural style where a software application is divided into small, independent services that can be developed, deployed, and scaled independently. It promotes modularity and flexibility.
38- Version Control
Version control, or source control, manages changes to source code over time. It allows multiple developers to collaborate, tracks changes, and provides the ability to roll back to previous versions if needed.
39- Framework
A framework is a pre-built structure or set of tools that provides a foundation for software development. It simplifies and accelerates the development process by offering reusable code and standard conventions.
40- Scripting Language
A scripting language is a programming language used to automate tasks, control software applications, and manipulate data. Examples include Python, Ruby, and PowerShell.
41- Endpoint
In networking, an endpoint is a specific address or location to which data can be sent or from which it can be received. In the context of APIs, an endpoint is a URL where an API can be accessed.
42- Raster and Vector Graphics
Raster graphics use pixels to represent images, while vector graphics use mathematical equations to define shapes. Understanding the difference is essential for tasks like graphic design and web development.
43- Load Balancing
Load balancing involves distributing network traffic across multiple servers to ensure optimal resource utilization, maximize throughput, and minimize response time. It improves the performance and reliability of applications.
44- Root Access
Root access, or administrative access, provides full control over a computer system. It allows users to modify system files and settings.
45- Latency
Latency refers to the delay between the initiation of a task and the occurrence of its first measurable effect. In IT, it often relates to the time it takes for data to travel between its source and destination.
46- Repository
A repository, commonly referred to as a repo, is a central storage location where version-controlled files and project assets are stored. Developers use repositories for collaborative and version-controlled software development.
47- SSL/TLS
SSL (Secure Sockets Layer) and TLS (Transport Layer Security) are cryptographic protocols that ensure secure communication over a computer network. They are commonly used to secure data transmission on the internet, such as in HTTPS.
48- Cookie
A cookie is a small piece of data stored on a user’s device by a web browsers. Cookies are used to track user interactions with websites, personalize content, and maintain session information.
49- Responsive Design
Responsive design is an approach to web design that ensures a website’s layout and content adapt to different screen sizes and devices. It provides an optimal viewing experience across various platforms, including desktops, tablets, and smartphones.
50- Docker
Docker is a platform for developing, shipping, and running applications in containers. Containers are lightweight, portable, and self-sufficient units that encapsulate an application and its dependencies, ensuring consistent deployment across different environments.
Conclusion
In conclusion, attaining basic knowledge about such essential IT terms gives new entrants an initial understanding of the vibrant field of technology. From digging into programming languages and learning the art of networking to dealing with development methodologies – these words are irreplaceable cores. Accepting ideas such as encryption, microservices and responsive design allows people to communicate both in a personal way and by contributing to work as part of a team while adapting to the ever-changing technology world. With the advent of technology working to create the future, handling these terms not only helps to integrate smoothly but also lets individuals understand and do well in all areas of IT. So, let us welcome you to the realm of IT where these terms act as catalysts in bringing innovation and continuous improvement.